Keycloak

Keycloak is an integrated SSO and IDM for browser apps and RESTful web services. Built on top of the OAuth 2.0, Open ID Connect, JSON Web Token (JWT) and SAML 2.0 specifications. Keycloak has tight integration with a variety of platforms and has a HTTP security proxy service where we don't have tight integration. Options are to deploy it with an existing app server, as a black-box appliance, or as an Openshift cloud service and\/or cartridge.
Features
- Single-Sign On: Login once to multiple applications
- Standard Protocols: OpenID Connect, OAuth 2.0 and SAML 2.0
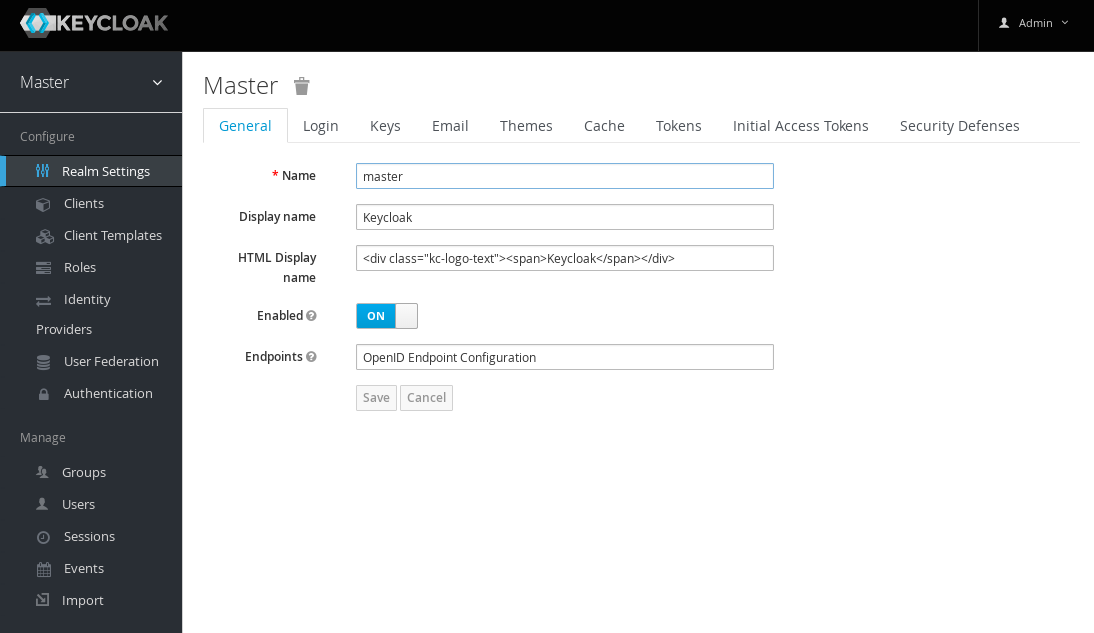
- Centralized Management: For admins and users
- Adapters: Secure applications and services easily
- LDAP and Active Directory: Connect to existing user directories
- Social Login: Easily enable social login
- Identity Brokering: OpenID Connect or SAML 2.0 IdPs
- High Performance: Lightweight, fast and scalable
- Clustering: For scalability and availability
- Themes: Customize look and feel
- Extensible: Customize through code
- Password Policies
Installation
A very simple way to setup Keycloak is Docker. JBoss provides an official image:
$ KEYCLOAK_USER=admin
$ KEYCLOAK_PASSWORD=admin
$ docker run -d --name keycloak \
-p 8080:8080 \
-e KEYCLOAK_USER=$KEYCLOAK_USER \
-e KEYCLOAK_PASSWORD=$KEYCLOAK_PASSWORD \
jboss/keycloak:latest
$ docker logs -f keycloak
This will setup a Keycloak instance using an emended database (H2). Once started you can browse to the admin console.